Affiliate Disclosure: This article may contain affiliate links. If you purchase through them, we may earn a small commission at no extra cost to you. This helps support our research and editorial work.
A decade ago, “remote work security” mostly meant using a strong password.
Today it means something entirely different.
Professionals now access sensitive files from coffee shops, airports, shared coworking spaces, and hotel Wi-Fi networks around the world. Cloud platforms store company data. Messaging apps replace internal networks. Meetings happen on laptops that constantly switch between networks.
Remote work unlocked unprecedented freedom, but it also created a quiet security crisis.
The problem is that many professionals still rely on outdated assumptions about internet safety. They believe if a website shows a lock icon, everything is secure.
Unfortunately, that belief leaves enormous gaps.
And cybercriminals have already figured it out.
The Hidden Danger of Public Wi-Fi Networks

Public Wi-Fi networks are convenient, fast, and everywhere.
They are also one of the easiest environments for cyber attackers to exploit.
Many networks in hotels, cafés, airports, and coworking spaces lack strong encryption. This makes it possible for attackers on the same network to intercept unprotected data moving between devices and websites.
Even when websites use HTTPS, other types of traffic may still be visible.
These attacks are often called “man-in-the-middle attacks,” and they can capture things like:
- Login credentials
- Session cookies
- Personal browsing activity
- Email metadata
- Corporate data requests
Most victims never realize anything happened.
Everything still works normally on their screen.
But in the background, someone else may already have access.
This is why cybersecurity experts frequently describe public networks as “the softest entry point into remote workers’ digital lives.”
Why Remote Workers Are a Prime Target

Cybercriminals rarely attack randomly.
They target environments where the reward is highest and the defenses are weakest.
Remote workers unfortunately fit that profile perfectly.
Here’s why.
First, remote professionals often have access to valuable corporate systems. A compromised laptop may provide entry to cloud storage, internal documents, or customer databases.
Second, remote work removes traditional office protections. Corporate networks often include firewalls, intrusion detection systems, and secure access gateways. Home and café networks rarely offer these layers.
Third, remote workers frequently switch networks throughout the day.
Each new connection creates another opportunity for interception.
That is why cybersecurity researchers often warn companies about “the invisible attack surface created by distributed work.”
The more locations employees connect from, the more potential entry points exist.
The Problem With Traditional Security Advice

Most security advice given to professionals focuses on familiar topics:
- Use strong passwords
- Enable two-factor authentication
- Keep software updated
These are important, but they only address part of the problem.
They protect accounts, not connections.
If your internet traffic travels through an insecure network, attackers may still observe or manipulate certain types of communication before it reaches its destination.
This is the part many professionals overlook.
Connection security matters just as much as account security.
Think of it like sending sensitive documents through the mail. Locking the envelope is helpful, but you also want to ensure the courier cannot open it along the way.
That is where encrypted network routing becomes valuable.
How Secure Tunneling Protects Remote Workers
Secure tunneling works by encrypting your internet traffic before it leaves your device.
Instead of sending data openly across the local network, everything travels through a protected channel to a secure server.
From there it continues to its destination.
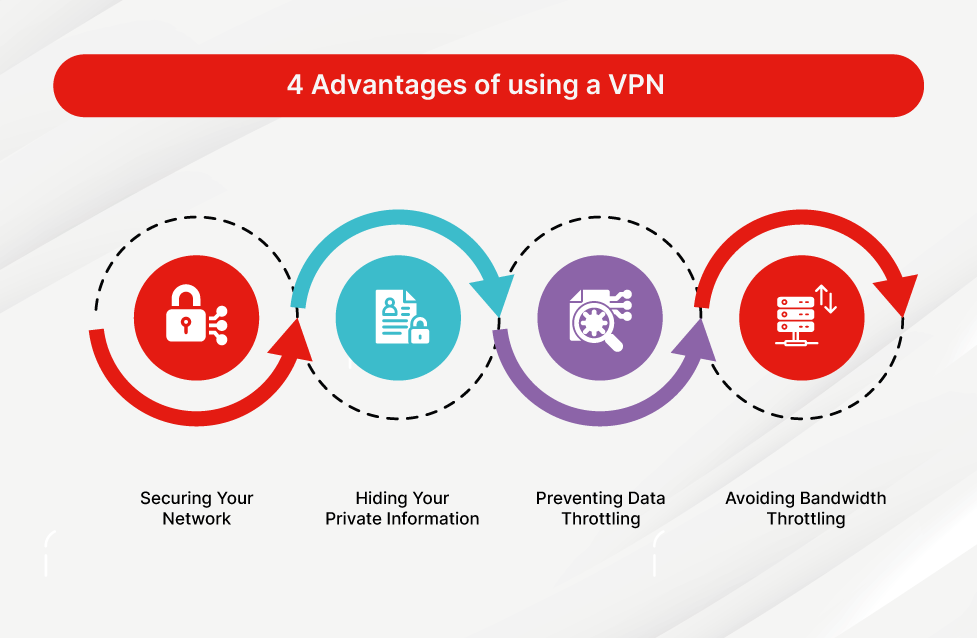
This process creates several benefits for remote professionals.
First, anyone monitoring the local Wi-Fi network cannot see the actual contents of the traffic.
Second, attackers cannot easily intercept or manipulate requests.
Third, your IP address and location are masked, which adds another layer of privacy.
Modern services like Surfshark specialize in creating these encrypted tunnels automatically across multiple devices.
For remote workers, this means the same protection applies whether they are working from a home office, a coworking space, or a hotel room overseas.
The result is what cybersecurity specialists often describe as “working on public Wi-Fi with private-network security.”
Why Location Privacy Matters More Than People Realize
Another overlooked risk involves location data.
Every time you connect to a website, your IP address reveals approximate information about your location and network.
For everyday browsing this may seem harmless.
For professionals, it can sometimes expose patterns about where and when they work.
Over time, this data can be used for tracking, targeted attacks, or profiling.
Encrypted routing tools reduce this exposure by replacing your visible IP address with that of the secure server you connect through.
Services like Surfshark allow professionals to select server locations across multiple regions, giving them greater control over how their digital footprint appears online.
It is a small technical change, but one that significantly improves privacy.
The Security Layer Most Remote Work Setups Are Missing
Strong remote security usually requires several layers working together.
Password managers protect accounts.
Two-factor authentication protects logins.
Antivirus protects devices.
But there is often one missing piece.
Network protection.
Without it, all the other layers rely on the assumption that the network itself is safe. In public environments, that assumption rarely holds.
Adding encrypted routing fills this gap.
That is why many cybersecurity professionals recommend privacy networks as part of a complete remote work toolkit.
Platforms such as Surfshark combine encrypted connections with additional features like tracker blocking and malware protection, creating a more comprehensive security environment for distributed work.
The New Reality of Professional Mobility

Work is no longer tied to a single building.
Professionals now operate from airplanes, cafés, shared offices, and temporary apartments around the world.
This flexibility is one of the greatest advantages of modern technology.
But mobility always introduces new risks.
The challenge is not avoiding remote work. It is adapting security practices to match this new reality.
For many professionals, that simply means upgrading from outdated assumptions about internet safety to tools designed for a distributed world.
Once secure connections become part of daily workflow, remote work begins to feel exactly the way it was meant to: flexible, efficient, and safe.
And with privacy solutions like Surfshark quietly protecting connections in the background, professionals can focus on their work instead of worrying about the network they happen to be using.